Table of Contents
- What Is Cybersecurity? Understanding Cybersecurity Fundamentals
- Cybersecurity Skills Guide for Beginners and Professionals
- Online Privacy Tools and Techniques to Prevent Cyber Attacks
- Network Security and Ethical Hacking Explained
- Cybersecurity Career Roadmap: From Beginner to Expert
- Building a Cybersecurity Roadmap for Long-Term Success
- Conclusion: Take Action to Protect Your Online Privacy
- FAQ for Cyber Security Guides
I want to be honest with you — when I first heard the word cybersecurity then I feel great interest about cybersecurity skills, I thought it was something only big tech companies needed to worry about. Then a friend of mine had his email account hacked, and suddenly all his contacts were getting phishing emails pretending to be from him. That one moment changed how I look at online safety completely. This cybersecurity skills guide is everything I wish I had back then — simple, clear, and actionable. Whether you’re just getting started or thinking about building a career in this field, I’ve got you covered. Let’s dive in the world of cybersecurity skills.
1. What Is Cybersecurity? Understanding Cybersecurity Fundamentals
What Is Cybersecurity and Why It Matters Today
So, what is cybersecurity, exactly? In simple terms, cybersecurity is the practice of protecting computers, networks, programs, and data from digital attacks, damage, or unauthorized access. It’s basically a digital shield that keeps your information safe from bad actors online.
You might wonder — why does this matter for regular people like me and you? Well, consider this: according to Cybersecurity Ventures, cybercrime is expected to cost the global economy over $10 trillion annually by 2025. That’s not just a number — those are real people losing real money and personal data every single day.
Furthermore, cyber threats are not just about big corporations. Everyday users face risks like:
- Phishing attacks — fake emails or messages designed to steal your passwords
- Data breaches — when companies lose your personal information to hackers
- Ransomware — malware that locks your files until you pay a ransom
- Identity theft — when criminals use your personal data to impersonate you
Therefore, understanding cybersecurity fundamentals is no longer optional. It’s a basic digital survival skill for everyone in 2026.
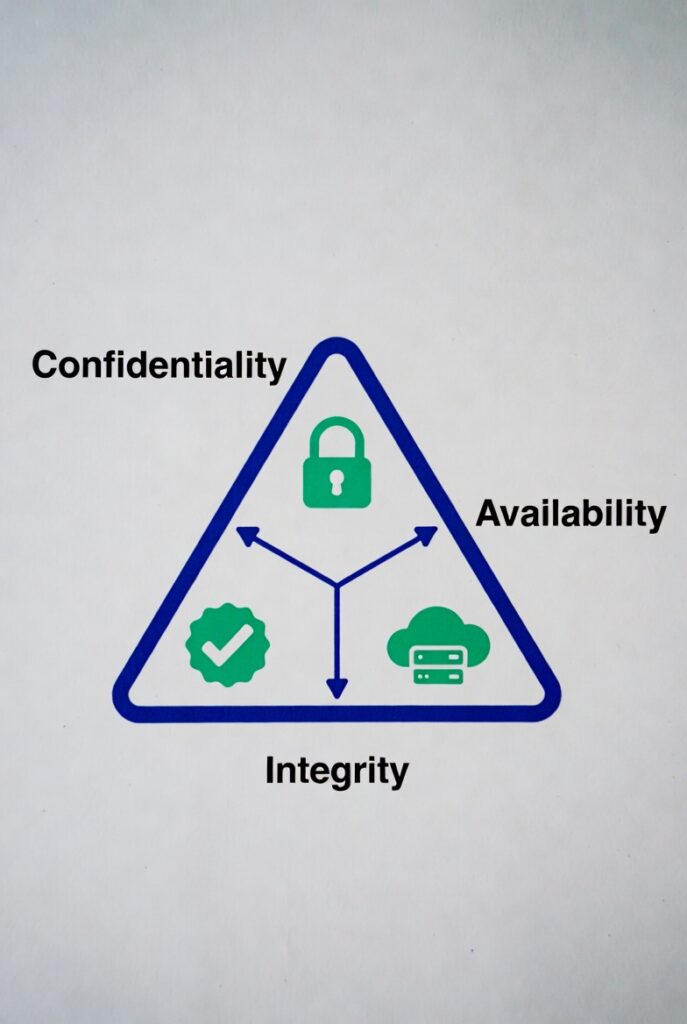
Core Cybersecurity Fundamentals Everyone Should Know
Before jumping into advanced tools and techniques, let’s cover some basic cybersecurity concepts that form the foundation of everything else.
The most important framework in cybersecurity is called the CIA Triad. However, it has nothing to do with spy agencies — it stands for:
- Confidentiality — making sure only authorized people can access your data
- Integrity — ensuring your data is accurate and hasn’t been tampered with
- Availability — making sure systems and data are accessible when you need them
In addition, you’ll often see the terms cyber security and cybersecurity used interchangeably. In practice, they mean the same thing — one is simply written as two words and the other as one compound word. Both refer to the same field of protecting digital systems.
Network security basics are also essential to understand. For example, firewalls act like digital bouncers — they decide what traffic is allowed in and out of your network. VPNs (Virtual Private Networks) encrypt your internet connection so nobody can snoop on what you’re doing online. If you’re new to these ideas, my beginner online safety guide is a great place to start building these habits.
2. Cybersecurity Skills Guide for Beginners and Professionals
Essential Cybersecurity Skills You Must Learn
Now let’s get into the heart of this cybersecurity skills guide — the actual skills you need to know.
First, risk assessment is everything. This means learning to identify potential threats and evaluate how much damage they could cause. It sounds technical, but in practice it’s as simple as asking: ‘What could go wrong, and how bad would it be?’
Next, threat detection is the ability to recognize when something suspicious is happening. For example, spotting a phishing email isn’t that hard once you know what to look for:
- Check the sender’s email address — is it slightly misspelled?
- Look for urgent language like ‘Your account will be closed immediately!’
- Hover over links before clicking — does the URL look legitimate?
- Be suspicious of unexpected attachments, even from people you know
Moreover, network security skills are vital for both personal use and professional roles. Understanding how firewalls work, how to configure a VPN, and how to secure a Wi-Fi network will take you far. These are also among the most in-demand skills for entry-level cybersecurity jobs.
Finally, ethical hacking fundamentals give you the ability to think like an attacker — which is exactly how defenders catch threats before they happen.
Advanced Skills for Cybersecurity Engineers
If you’re aiming for a cybersecurity engineer role, you’ll need to go deeper. Here’s what professionals in the field focus on:
- Penetration testing — simulating real-world attacks to find vulnerabilities before hackers do
- Security automation — writing scripts (often in Python) to detect and respond to threats faster
- Incident response — knowing exactly what to do when a security breach occurs
- Cloud security — protecting data and systems hosted on platforms like AWS, Azure, or Google Cloud
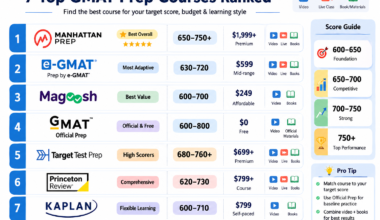
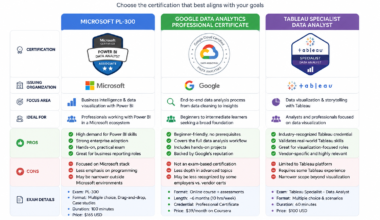
Furthermore, certifications matter a lot in this field. The most recognized ones include:
- CompTIA Security+ — best for beginners, widely recognized by employers
- CEH (Certified Ethical Hacker) — focused on offensive security skills
- CISSP (Certified Information Systems Security Professional) — advanced, for experienced pros
However, don’t feel pressured to get all of them at once. In fact, starting with just one — like CompTIA Security+ — is often the best move. I’ll cover the full certification roadmap in detail later in this guide.
3. Online Privacy Tools and Techniques to Prevent Cyber Attacks

Best Online Privacy Tools for Personal Data Protection
There are a ton of tools out there, and it can be overwhelming. So let me break it down into categories that actually matter for everyday use.
VPNs (Virtual Private Networks) are your first line of defense when browsing online, especially on public Wi-Fi. They encrypt all your internet traffic so even your internet service provider can’t see what you’re doing. Some popular options include NordVPN, ExpressVPN, and Proton VPN.
Password managers solve one of the biggest human problems in cybersecurity — reusing weak passwords. Tools like Bitwarden (free and open-source), 1Password, and Dashlane generate strong unique passwords and store them securely. You only need to remember one master password.
Antivirus software provides real-time protection against malware, ransomware, and other threats. However, modern operating systems like Windows 11 include built-in protection (Windows Defender) that’s actually quite solid for most users. Additional options like Malwarebytes offer a free tier for extra scanning.
For secure communication, encryption tools like Signal (for messaging) and ProtonMail (for email) ensure that only you and your recipient can read your messages. As a result, even if someone intercepts the data, they won’t be able to decode it.
Practical Internet Security Tips to Stay Safe
In addition to tools, your habits matter just as much. Here’s a simple checklist to follow:
- Use strong, unique passwords for every account (your password manager handles this)
- Enable Two-Factor Authentication (2FA) on every important account — email, banking, social media
- Keep your software and operating system updated — patches fix known security holes
- Be cautious on public Wi-Fi — use a VPN if you must connect
- Regularly back up your data — use both cloud and local storage
- Review app permissions on your phone — does that flashlight app really need access to your contacts?
- Use a private/incognito browser mode when researching sensitive topics
Moreover, think twice before clicking any link in an email, text message, or social media post. This single habit prevents the majority of phishing attacks. Therefore, developing a ‘pause before you click’ mindset is one of the most powerful free security tools you have.
4. Network Security and Ethical Hacking Explained

How Network Security Protects Your Data
Think of your network as a house. Network security is everything that keeps intruders out — the locks, the alarm system, the security cameras. Let’s look at the key components:
- Firewalls — monitor and filter incoming and outgoing traffic based on security rules
- IDS/IPS (Intrusion Detection/Prevention Systems) — automatically detect and block suspicious activity
- Network segmentation — dividing a network into smaller parts so a breach in one area doesn’t spread
- Encryption protocols — like HTTPS and TLS, which protect data in transit
However, network security isn’t just for enterprises. Your home network needs attention too. For example, here’s how to make your home Wi-Fi more secure:
- Change the default router username and password immediately
- Use WPA3 encryption (or at least WPA2) — never WEP, which is outdated and easily cracked
- Disable remote management unless you specifically need it
- Create a separate guest network for visitors and smart home devices
- Regularly check which devices are connected to your network
Ethical Hacking: Prevent Cyber Attacks Before They Happen
Ethical hacking — also called penetration testing or white-hat hacking — is the practice of legally breaking into systems to find their weaknesses before malicious hackers do.
Here’s a real-world scenario: imagine a company hires an ethical hacker to test their systems. The ethical hacker runs a penetration test and discovers that the company’s employee login portal is vulnerable to a brute-force attack. They report this to the company, which fixes the vulnerability. As a result, a real attacker never gets the chance to exploit it.
Furthermore, ethical hacking is a legitimate and well-paying career path. Cybersecurity engineers with penetration testing skills are in massive demand globally. Tools commonly used include Kali Linux (a security-focused Linux distribution), Metasploit (for testing exploits), Nmap (for scanning networks), and Wireshark (for analyzing network traffic).
If you’re curious about how AI is changing the security landscape, I’d recommend reading about
AI skills for 2026 including security automation — it covers how machine learning is reshaping cybersecurity threat detection.
5. Cybersecurity Career Roadmap: From Beginner to Expert

Cybersecurity Career Path and Opportunities
I’ll be straight with you — cybersecurity is one of the most exciting career fields right now. The demand is massive, the salaries are strong, and the work is genuinely meaningful. You’re literally helping protect people and organizations from real threats.
Here are the main roles you can aim for, roughly in order of experience level:
- Security Analyst (Entry-level) — monitors systems for threats, responds to alerts, runs reports
- Cybersecurity Engineer (Mid-level) — builds and maintains security infrastructure, writes automation scripts
- Penetration Tester / Ethical Hacker (Mid to Senior) — simulates attacks to find vulnerabilities
- Security Architect (Senior) — designs the overall security strategy for an organization
- CISO (Chief Information Security Officer) — leads the entire security team and strategy at the executive level
In terms of salary, the U.S. Bureau of Labor Statistics reports that information security analysts earn a median annual salary of around $120,000 in the United States. However, salary varies significantly by location, specialization, and experience. Furthermore, the field is projected to grow at 32% over the next decade — much faster than average.
Moreover, the cybersecurity job market is truly global. Remote work has made it possible to work for companies in the U.S., Europe, or Australia while living anywhere in the world. This is great news if you’re in a market like Bangladesh and want to access international opportunities.
Cybersecurity Certification Roadmap
Certifications are your fastest path to credibility in cybersecurity — especially if you’re self-taught or new to the field. Here’s a structured certification roadmap:
Entry-Level (Start Here):
- CompTIA Security+ — the gold standard for beginners; covers core security concepts and is recognized worldwide
- Google Cybersecurity Certificate — a beginner-friendly course available on Coursera, ideal for absolute newcomers
- CompTIA Network+ — optional but useful; helps you understand networking before diving into security
Intermediate Level:
- CEH (Certified Ethical Hacker) — focuses on offensive security and penetration testing techniques
- CISSP (Certified Information Systems Security Professional) — comprehensive and widely respected; requires 5 years of experience
- eJPT (eLearnSecurity Junior Penetration Tester) — great hands-on certification for aspiring pentesters
Advanced Level:
- AWS Certified Security Specialty — for cloud security professionals working with Amazon Web Services
- OSCP (Offensive Security Certified Professional) — the most respected hands-on penetration testing certification
- CISM (Certified Information Security Manager) — for those moving into leadership and management roles
For a broader look at top credentials across all of IT, check out my post on the
best IT certifications for 2026 — it covers both technical and management tracks.
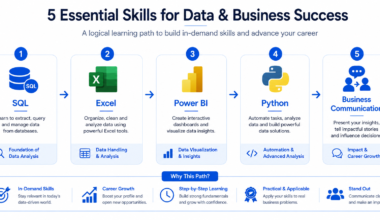
6. Building a Cybersecurity Roadmap for Long-Term Success
Step-by-Step Cybersecurity Learning Roadmap
One of the biggest mistakes I see beginners make is jumping around from topic to topic with no clear plan. So let me give you a simple, time-tested learning roadmap that actually works.
Phase 1 — Beginner (Months 1–3):
- Learn basic networking: how the internet works, IP addresses, DNS, TCP/IP
- Study for and earn CompTIA Security+ or the Google Cybersecurity Certificate
- Set up a home lab using free tools like VirtualBox and Kali Linux
- Practice on free platforms: TryHackMe (absolute beginner-friendly) and Cybrary
Phase 2 — Intermediate (Months 4–6):
- Learn scripting basics in Python — automation is essential in modern cybersecurity
- Start practicing ethical hacking challenges on Hack The Box
- Study for the CEH or eJPT certification
- Build a portfolio: document your learning, write about the challenges you’ve solved
Phase 3 — Advanced (Months 7–12):
- Specialize in an area: cloud security, penetration testing, threat intelligence, or security engineering
- Pursue advanced certifications like OSCP or CISSP
- Apply for entry-level roles or freelance security consulting gigs
- Contribute to open-source security projects to build real-world credibility
In addition, if you want to understand how AI fits into modern skill-building, my post on
how to use ChatGPT for learning and prompt engineering shows how to use AI tools to study faster and more effectively.
Common Mistakes to Avoid in Cyber Security Learning
Now, let me save you from some painful learning mistakes I’ve seen people make over and over again.
Mistake #1: Skipping Fundamentals. I know tools and hacking look exciting, but if you don’t understand how networks and operating systems work, you won’t understand WHY those tools do what they do. Therefore, invest time in the basics first. Everything else becomes much easier after that.
Mistake #2: Over-Relying on Tools Without Understanding Them. Running Nmap or Metasploit without understanding what they’re doing is like driving a car without knowing how brakes work. However, tools are powerful when you understand their logic — so always learn the ‘why’ behind the ‘how’.
Mistake #3: Not Practicing Real-World Scenarios. Reading textbooks is useful, but cybersecurity is a hands-on field. As a result, platforms like TryHackMe and Hack The Box exist precisely for this reason — use them regularly. Even 30 minutes a day of practical practice beats 5 hours of passive reading.
Mistake #4: Ignoring Soft Skills. Communication, report writing, and the ability to explain technical risks to non-technical stakeholders are hugely underrated. In fact, many senior cybersecurity roles require as much communication skill as technical skill. So, work on both sides.
7. Conclusion: Take Action to Protect Your Online Privacy
We’ve covered a lot of ground in this cybersecurity skills guide, so let me quickly summarize the key takeaways.
Cybersecurity is not just for IT professionals — it’s a skill every digital citizen needs in 2026. Understanding the fundamentals (like the CIA Triad and network security basics) gives you a solid foundation. Furthermore, adopting the right online privacy tools — VPNs, password managers, 2FA — dramatically reduces your risk of being attacked.
If you’re thinking about a career in cybersecurity, the path is clearer than ever. Start with a beginner certification like CompTIA Security+, build hands-on skills through home labs and platforms like TryHackMe, and progress through the certification roadmap at your own pace. The demand for cybersecurity professionals is only growing, and the field rewards those who are consistent and curious.
However, more than anything else — start today. You don’t need to become a cybersecurity engineer overnight. Instead, pick one thing from this guide, implement it right now, and build from there. Change your weakest password, set up 2FA on your email, or download Bitwarden. One step at a time.
Your online safety is worth protecting. I hope this guide gives you the confidence and clarity to take that first step. Let’s go!
8. FAQ asked for Cyber Security Learning
What is cybersecurity in simple terms?
Cybersecurity is the practice of protecting computers, networks, devices, and personal data from hackers, malware, phishing scams, and other digital threats.
Why is cybersecurity important for everyday users?
Cybersecurity matters because anyone can become a target of phishing, identity theft, ransomware, or data breaches. Even simple habits like using strong passwords can reduce your risk.
What are the most important cybersecurity skills to learn first?
The best beginner cybersecurity skills include risk assessment, password management, phishing detection, network security basics, and using privacy tools like VPNs and antivirus software.
What is the difference between cyber security and cybersecurity?
There is no real difference. “Cyber security” and “cybersecurity” mean the same thing. One is written as two words, while the other is written as one.
How can I protect my online privacy?
You can protect your online privacy by using strong passwords, enabling two-factor authentication, using a VPN, updating your software regularly, and avoiding suspicious links.
What is ethical hacking?
Ethical hacking is the legal process of testing systems, networks, or applications to find vulnerabilities before real hackers can exploit them.
What does a cybersecurity engineer do?
A cybersecurity engineer builds and manages security systems, protects networks, responds to threats, and helps prevent cyber attacks within an organization.
Which cybersecurity certification should beginners start with?
Most beginners should start with certifications like CompTIA Security+ or the Google Cybersecurity Certificate because they cover the basics and are widely recognized.
Is cybersecurity a good career choice?
Yes. Cybersecurity is one of the fastest-growing fields, with strong salaries, global job demand, remote work opportunities, and multiple career paths such as analyst, engineer, and ethical hacker.